The App at a Glance.
Real alerts, real networks — screenshots captured from a live CYJAN IDS deployment.
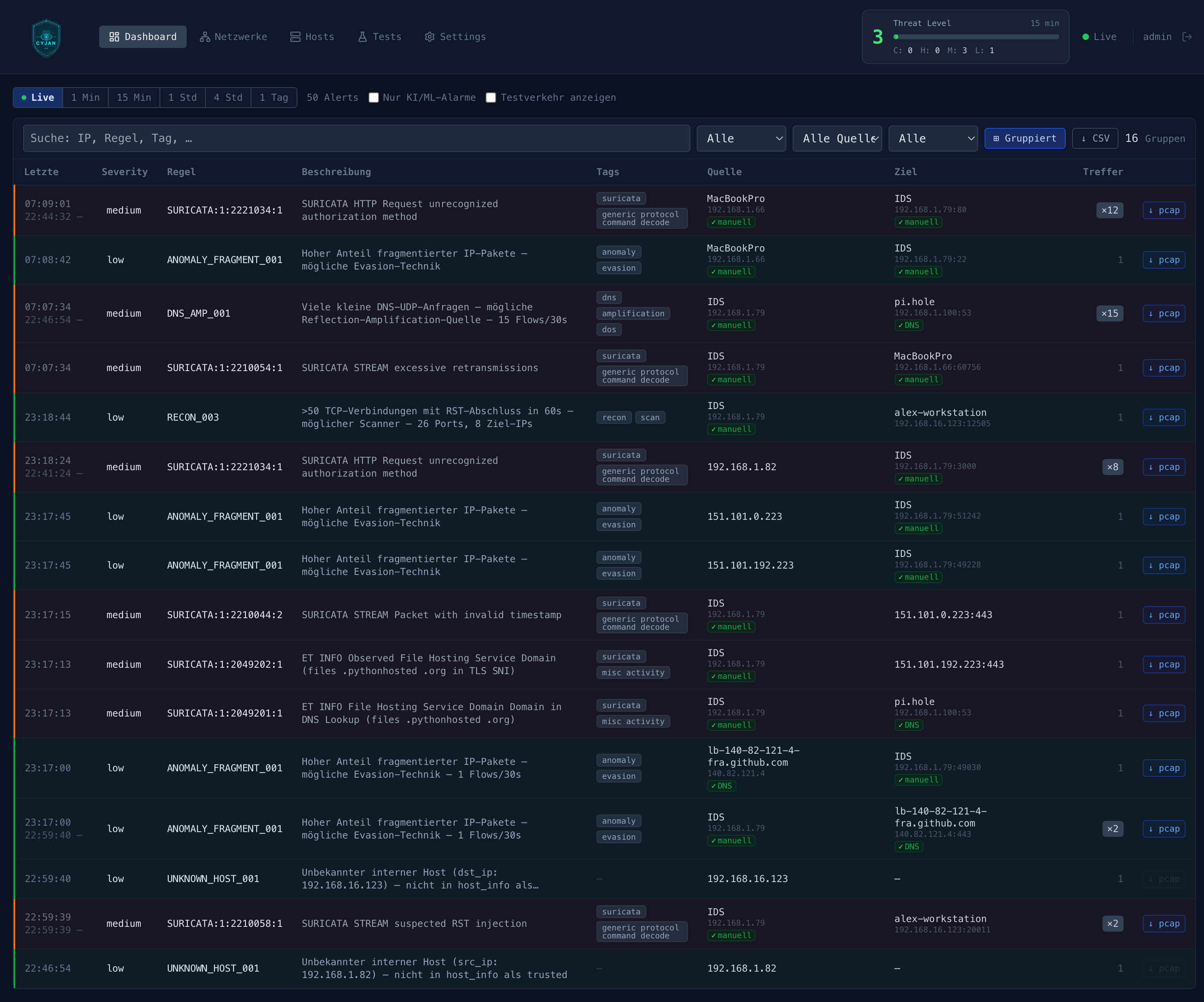
Real-time WebSocket stream of every alert — severity, source, destination, tags, and one-click PCAP download.
Live aggregated threat index — critical / high / medium / low breakdown for an instant read on network health.
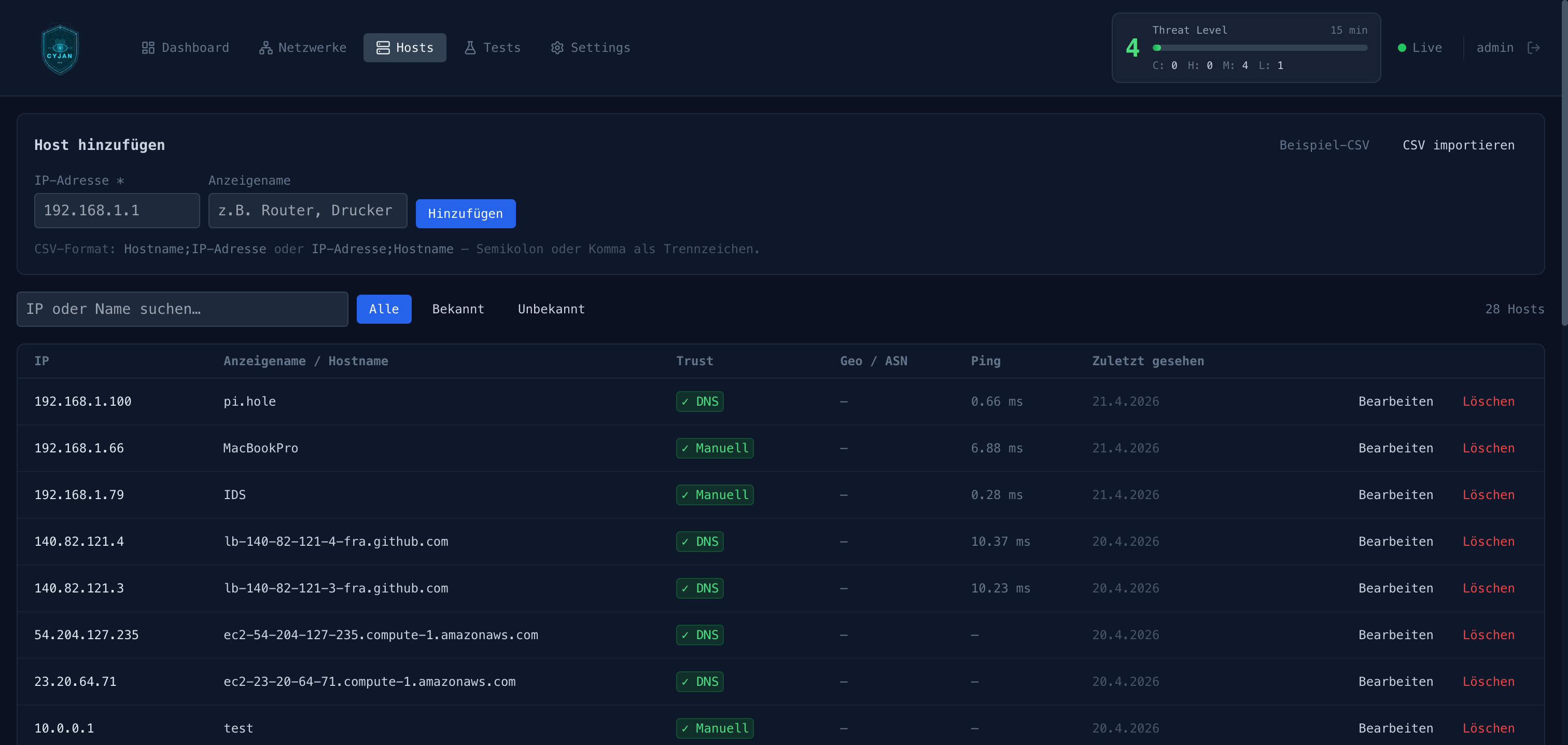
Every host auto-enriched via DNS and GeoIP — unknown devices trigger an alert the moment they appear.